Over 900k users were hit by malicious Chrome extensions posing as ChatGPT and DeepSeek tools. We dive deep into the analysis, the C2 exfiltration, and how to secure your browser....
What’s Next? Leveraging Your Cyber Security Home Lab for Mastery
Congratulations! If you are reading this, you have likely finished setting up your cyber security home lab.
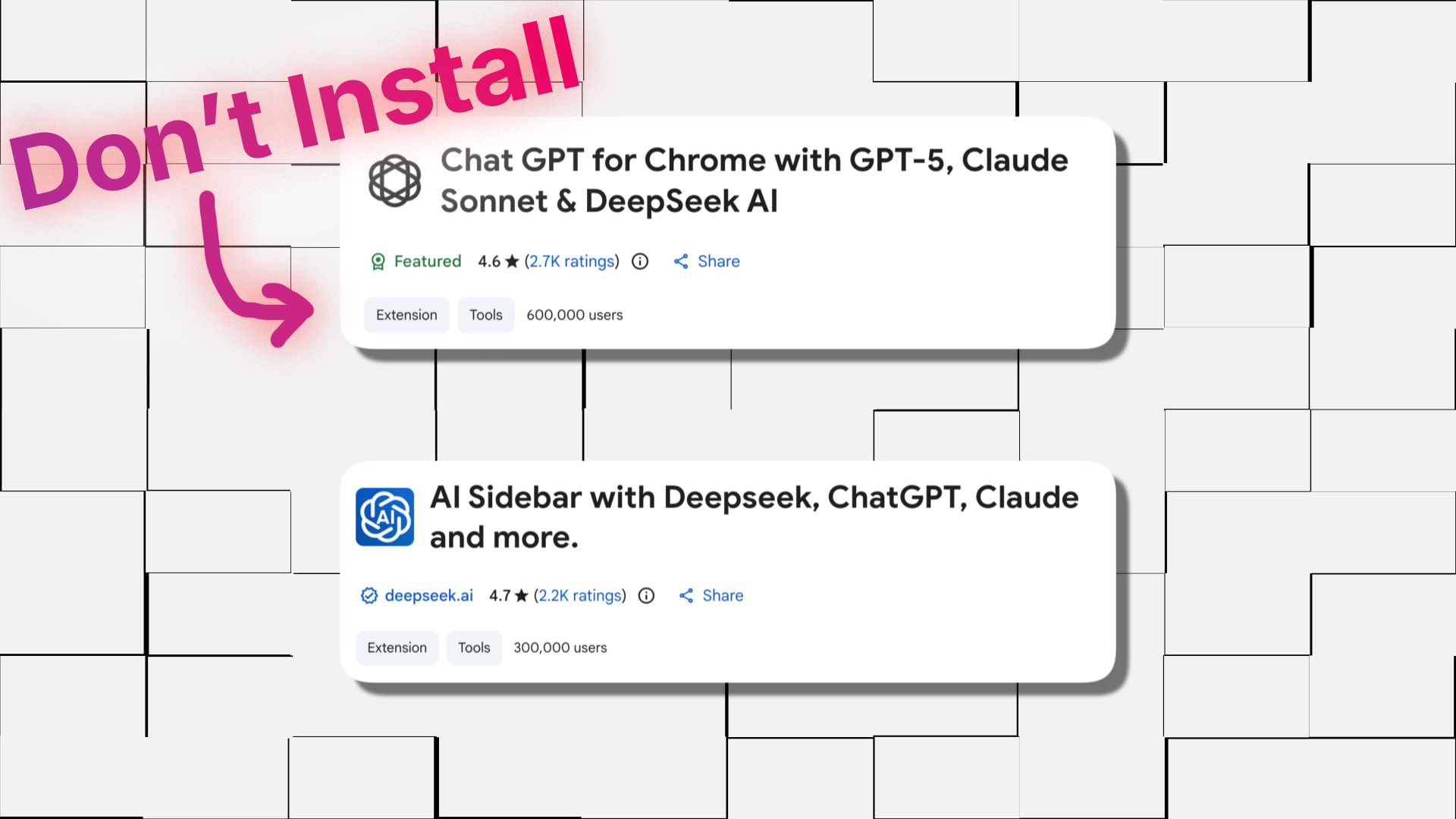
How Malicious Chrome Extensions Exposed 900K Users This December ?
Over 900k users were hit by malicious Chrome extensions posing as ChatGPT and DeepSeek tools. We dive deep into the analysis, the C2 exfiltration, and how to secure your browser.

How to Install WSL and Docker For Cyber Security Homelab ?
In this part, we are going to install WSL and Docker on our machine. If you don't have a high-configuration computer at your hands,
How To Create Your First Virtual Machine In 2025?
In this blog, I'm going to show you how you can create your first virtual machine with VMware. At first, the virtualization concept and the thought of creating your first virtual machine might seem a little complex, but in reality, it is really, really simple.
How To Download VMware Workstation and ISOs ?
In this part, we are going to see how you can download the virtualization software VMware and the ISOs that you are going to need for creating your own homelab.
What Are The Requirements For Your Own Cyber Security Homelab ?
Before we get our hands dirty with HomeLab setup its important to know what type of hardware you currently have and what you will need throughout this series.

You need to setup your Cyber Security HomeLab RIGHT NOW‼️
From this blog post our new journey begins. We're going to set up our own cybersecurity home lab In which you can do anything you want.
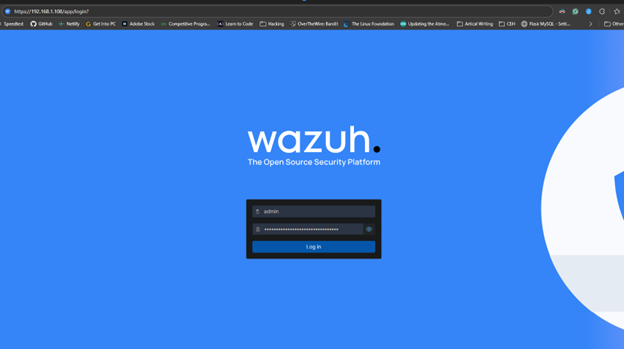
How to Install Wazuh on Raspberry Pi ?
Let's, Install Wazuh server on a raspberry Pi. In this blog, I will give you a step-by-step installation process of Wazuh server on raspberry pi.
Cloud Network Security Strategies You Are Missing !!
Discover engaging, real-world “Cloud Network Security Strategies” that balance Zero Trust, micro-segmentation, encryption, and compliance

How to Build a Resilient Network Security Architecture ?
Network Security isn’t just a buzzword – it’s the foundation of protecting your network and data.
